Introduction
Thinking about bringing in an outside team for year-end verification, a multi-site cleanup, or a post-acquisition asset baseline? This guide explains what outsourced asset verification involves, how asset verification and tagging services work, what a competent provider should deliver, and when outsourcing strengthens control rather than creates confusion.
Fixed asset verification services are outsourced programs that help an organization plan, execute, document, and close a physical verification cycle. The best providers do more than count assets: they clean the starting data, execute a complete on-site fixed asset verification process using established best practices, reconcile field results against records, structure outputs for ERP/CMMS handoff, and produce audit-ready documentation.
In this guide, you’ll learn:
- What fixed asset verification services actually include, and how fieldwork, records, and reporting come together into a complete cycle.
- Why organizations turn to outsourced asset verification, especially when assets are spread across locations or internal bandwidth is limited.
- How to evaluate providers and their deliverables, so you can choose a model that fits your control environment rather than complicates it.
- Finally, when outsourcing works best and when a hybrid or in-house approach makes more sense, depending on your asset base and governance maturity.
What fixed asset verification services include?

A proper outsourced verification engagement should cover the whole chain from messy starting data to usable closeout. On AssetCues’ services page, that chain includes pre-verification cleanup, classification into taggable / verify-only / non-verifiable groups, onsite verification and tagging via mobile capture, reconciliation and validation, ERP/CMMS data structuring, and audit-ready documentation. Competitor service pages describe similar building blocks: deliverables such as register reports, certificates, condition reports, cross-location reconciliation, and exception reporting.
Scope stack buyers should expect
Workstream |
What a competent provider should do |
What the buyer should receive |
|---|---|---|
| Pre-verification cleanup | Review the baseline register, invoices/POs where needed, site lists, and scope assumptions | Cleaned source population, exclusions list, site plan |
| Planning | Define asset classes, methods, tag standards, access windows, and field rules | Approved project plan, tagging spec, evidence rules |
| On-site verification | Verify assets physically, capture required fields, record exceptions, and tag where in scope | Verified field data, tag manifest, exception captures |
| Reconciliation | Match field results to existing records and classify mismatches | Discrepancy log, matched schedule, not-found/additional/relocated lists |
| Reporting | Turn findings into management and audit-ready outputs | Summary report, location-wise outputs, condition list, action tracker |
| Data handoff | Structure final data for the systems that must be updated | ERP/CMMS-ready files, mapping notes, upload-ready handoff pack |
Original contribution: You can outsource fieldwork, not accountability
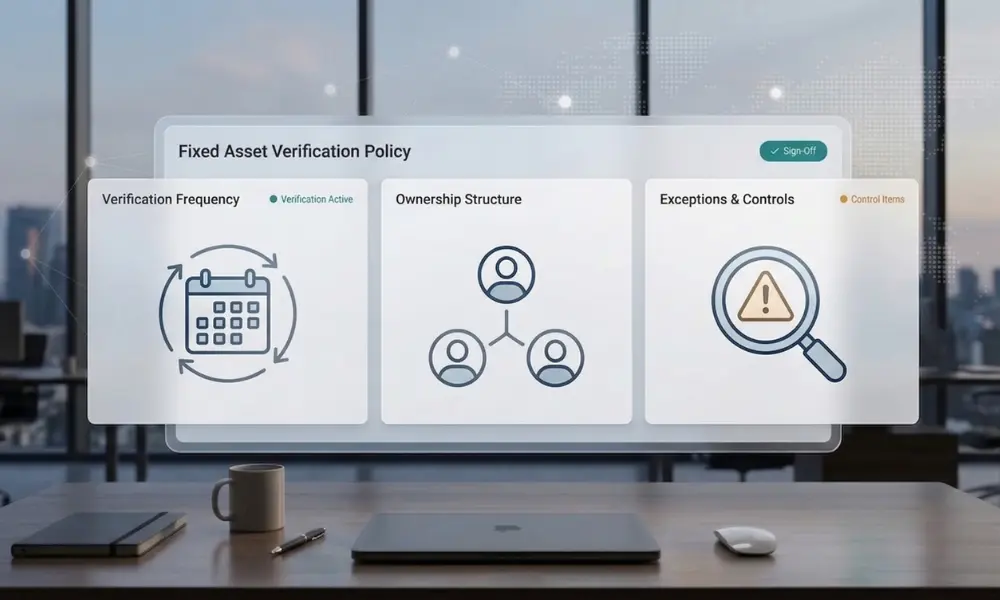
This is the most important distinction buyers usually miss. An external provider can perform fieldwork, tagging, reconciliation prep, and reporting support. However, management still owns the internal-control environment, the policy, the approval of material discrepancies, and the final accounting treatment. SEC rules put responsibility for internal control over financial reporting on management.
CARO language focuses on physical verification by management at reasonable intervals and on whether material discrepancies were properly dealt with in the books. The UK Corporate Governance Code likewise places the internal-control framework and annual review of effectiveness under board/management responsibility.
Execution vs accountability matrix
Task |
The provider can do it |
Management should retain accountability |
|---|---|---|
| Clean the starting register and site scope | Yes | Yes, approve final scope |
| Verify and tag assets in the field | Yes | Yes, approve methods and evidence rules |
| Build discrepancy logs and reports | Yes | Yes, review material findings |
| Recommend write-offs, transfers, or updates | Yes | Yes, approve book treatment and final updates |
| Prepare ERP/CMMS-ready data files | Yes | Yes, control the final post/update process |
| Support audit queries | Yes | Yes, own the representation and sign-off |
That distinction is not anti-outsourcing. It is what makes outsourcing safer. The best service providers make ownership clearer, not fuzzier.
When should you outsource?
Outsourcing makes sense when the organization needs execution scale, specialist structure, or independent validation that internal teams cannot provide quickly enough. AssetCues’ own takedown-listed company-selection article names the clearest triggers: limited internal resources, distributed assets, audit/compliance pressure, and a need for barcode/RFID-led execution. Its service page adds more commercial use cases: annual financial close verification, baseline creation, M&A, lender/insurer requirements, and valuation or revaluation support.
A practical outsourcing fit table
Situation |
Best fit |
Why |
|---|---|---|
| 30+ sites, multiple asset classes, tight deadline | Full-service outsourcing | You need field scale, project governance, and clean closeout |
| The internal team knows the estate well but lacks project structure | Hybrid | Site knowledge stays internal while the provider brings process and tooling |
| Weak register after years of drift | Full-service or structured hybrid | Cleanup, classification, and reconciliation matter as much as counting |
| M&A integration or ERP migration | Outsourced specialist support | You need baseline rebuilding, structured outputs, and faster closeout |
| Small single-site annual cycle with a disciplined team | In-house or software-led | External field capacity may be unnecessary |
| Continuous annual program with strong internal controls | Hybrid or software-led internal | Outsource spikes or special projects, not every routine cycle |
The most common outsourcing triggers
-
Multi-location rollout.
Once plants, branches, campuses, depots, or warehouses multiply, internal teams often struggle to keep scope, evidence rules, and timing consistent. AssetCues explicitly positions its service as scalable from single-site work to nationwide rollouts.
-
Audit pressure or limited bandwidth.
When year-end, statutory audit, lender review, or insurance validation arrives, finance teams often need verified records faster than internal field teams can produce them. AssetCues’ services page and the older vendor-selection article both frame outsourcing around audit-ready outputs and capacity constraints.
-
Register rebuilds, M&A, or ERP migration.
These projects usually require more than field checks. They require pre-verification cleanup, duplicate handling, classification, and system-ready handoff. AssetCues states those phases directly, including invoice/PO-backed cleanup and ERP/CMMS-ready outputs.
-
Lender, insurer, or valuation support.
AssetCues explicitly positions verification services for lender/insurer requirements and valuation/revaluation scenarios. In those cases, field proof and report quality often matter more than raw count speed.
When should you not outsource—and when is hybrid better?
Not every organization should outsource. That is an important credibility point, and your checklist explicitly asks for a balanced, honest tone.
You probably do not need a large outsourced engagement when the asset base is relatively stable, the estate is concentrated, the register is already clean, and the company already has disciplined site owners plus a repeatable annual routine. In those cases, software-led internal execution or a light hybrid model often makes more sense than buying a full field team.
Likewise, do not outsource a broken governance model. If the fixed asset physical verification policy, approval guidelines, ownership rules, or exception handling are undefined, the provider may deliver a clean field file, but the organization will still struggle to close findings properly. Outsourcing solves execution bottlenecks better than governance vacuums.
Delivery models compared
AssetCues’ service explicitly offers full-service or individual tagging, verification, or reconciliation solutions. That makes a model-comparison section essential.
Model |
Best for |
What the provider handles |
Main caution |
|---|---|---|---|
| Full-service | Large, distributed, or one-time cleanup projects | Cleanup, fieldwork, tagging, reconciliation, reporting, data handoff | Strong governance needed around approvals and access |
| Hybrid | Companies with capable site teams but limited central project bandwidth | Method, tooling, QA, reporting, and selected field support | Requires a very clear RACI |
| Project-based | M&A, audit-season cleanup, baseline creation, one-time catch-up | Defined-scope execution with formal closeout | Improvements can fade if BAU controls remain weak |
| Recurring program support | Annual or cyclical verification across many sites | Repeatable cadence, recurring evidence pack, structured handoff | Needs a long-term owner on the client side |
Services vs Software vs Hybrid
A service engagement gives you people, field execution, and project delivery. Software gives you a platform for repeatable internal cycles. Hybrid models combine both. AssetCues’ software page emphasizes discrepancy handling and register reconciliation, while the services page emphasizes field delivery, audit-ready documentation, and system handoff. That difference is exactly why this blog should help buyers choose the right operating model rather than just pitch one.
What deliverables should buyers ask for?
This is where many RFPs stay too vague. “Provide final report” is not enough. Ask for a deliverable pack with clear acceptance criteria.
Minimum deliverables checklist
Deliverable |
Why it matters |
Acceptance question |
|---|---|---|
| Approved scope and exclusions note | Prevents scope disputes later | Does it clearly list sites, asset classes, thresholds, and exclusions? |
| Cleaned the source population | Gives the project a controlled baseline | Can finance trace this file back to the register version used? |
| Verified asset-level output | Supports record-level review | Does it include asset ID, serial/tag, location, condition, and status? |
| Tagging manifest (if tagging is in scope) | Proves what was tagged and how | Does it list tag numbers, asset mapping, and tag type/spec? |
| Discrepancy log | Turns field findings into actions | Does it classify not found, additional, relocated, damaged, duplicate, and exception items? |
| Location-wise / site-wise reports | Helps operations and facilities act locally | Can site owners review their own exceptions quickly? |
| Damaged / idle/obsolete list | Supports maintenance, disposal, and impairment review | Are condition codes and next-action recommendations included? |
| Management summary | Gives leadership a decision-ready overview | Are counts, values, top risks, and action owners visible? |
| ERP/CMMS-ready handoff file | Speeds system closeout | Is the output mapped to the target fields and import format? |
| Sign-off and closeout pack | Preserves accountability | Are approvals, open items, and due dates clearly documented? |
Wishtree explicitly markets inventory reports, verification certificates, tagging, and condition reports. MBG highlights reconciliation, verification/exception reports, and audit documentation. South African public-entity specifications often require location reports, missing or damaged schedules, register-to-trial-balance support, and sometimes proposed journal entries. That is exactly why understanding what goes into a physical asset verification report format with findings and audit trail documentation matters before signing any contract — a vague “final report” clause almost always leads to disappointment.
Original contribution: What should go into the SOW and SLA?
Most buyer guides stop at “compare services and pricing.” That is not enough. The real commercial risk usually sits in the SOW and SLA.
Scope-to-SLA matrix
Clause |
What the SOW or SLA should define |
Why it matters |
|---|---|---|
| Sites and access windows | Site list, work hours, escort/safety rules, blocked zones | Prevents delays and false “not found” results |
| Asset scope | Classes, thresholds, exclusions, leased/third-party items, exception populations | Prevents scope drift |
| Method | File-to-floor, floor-to-book, wall-to-wall, or hybrid | Aligns expectations and evidence quality |
| Evidence standard | Required fields, photos, geotags, condition rules, alternate controls | Stops inconsistent field capture |
| Tagging spec | Barcode/QR/RFID type, durability, placement rules, and printing ownership | Prevents rework and tag mismatch |
| Discrepancy categories | Controlled reason codes and escalation owners | Speeds reconciliation and review |
| Reporting pack | Summary report, logs, annexures, site reports, action tracker | Prevents weak closeout |
| Data handoff | ERP/CMMS format, field mapping, test file, acceptance criteria | Prevents post-project cleanup pain |
| Rework window | Who handles disputed items, how many rechecks, by when | Keeps exceptions from lingering |
| Approval model | Who approves write-offs, additions, location changes, and final sign-off | Protects governance |
A buyer does not need a 40-page contract to get this right. However, the buyer does need these clauses stated clearly.
How should you compare providers?
Use a buyer-side evaluation scorecard to objectively assess providers across coverage, methodology, deliverables, integration, governance, sector experience, support, and pricing.
Buyer-side evaluation scorecard
Category |
What to test |
What a strong answer looks like |
|---|---|---|
| Field coverage | Can they mobilize across your geography and site profile? | Clear staffing model, rollout logic, and site-readiness assumptions |
| Method and evidence | How do they verify, classify, and retain proof? | Controlled method, evidence fields, and exception logic |
| Deliverables | What exact outputs do they provide? | Sample logs, summary pack, location reports, data handoff |
| Integration | Can they hand off data to ERP/CMMS/FAR cleanly? | Mapped import format, test file, and post-project support |
| Governance | Who owns approvals and sign-off? | Clear RACI, escalation path, and change-control process |
| Sector fit | Have they handled similar asset environments? | Relevant examples by asset class and operating environment |
| Post-project support | What happens after final fieldwork? | Recheck/rework window, closeout support, and handoff clarity |
| Commercial structure | What is included in the price? | Transparent assumptions, exclusions, and change-order rules |
AssetCues’ own services page gives buyers several of the proof points they should ask any provider to produce: flexible service models, ERP/CMMS integration, audit-ready documentation, multi-location scale, and visible industry/customer proof.
Red flags when selecting a provider
- They promise a “final report,” but cannot show a sample discrepancy log.
- They want to update the register directly without clear client approvals.
- They price cheaply by excluding rechecks, blocked-access zones, or data cleanup.
- They cannot define how outputs will map into ERP, CMMS, or the fixed asset register.
- They rely on vague evidence standards such as “where feasible” or “as available.”
- They have field capacity but no closeout discipline.
- They speak only about counting speed and not about exception handling, reporting, or action ownership.
Those red flags matter because weak closeout often creates more hidden costs than the initial service fee.
Country-specific buying notes

→ USA: Keep project governance tied to internal-control evidence
US buyers should consider the provider’s field strength while ensuring management maintains a clear trail of scope, evidence, exceptions, and remediation to meet annual ICFR requirements on responsibility, evaluation framework, and effectiveness. The outsourced team can strengthen execution, but the governance wrapper still belongs to management.
Useful US angle: A 20-site manufacturer needing independent field support before year-end close and walkthroughs.
→ India: Prioritize audit-season capacity and discrepancy treatment in books
India-focused service models should support clearly defined “reasonable intervals,” structured handling of material discrepancies, and a clean documentation pack ready for management and auditors. Buyers should therefore ask how the provider will support class-wise discrepancies, evidence retention, and book-treatment follow-up after fieldwork. MBG’s service positioning and CARO guidance both reinforce that audit-facing reality.
Useful India angle: A multi-plant rollout ahead of a statutory audit where register drift and missing-location detail have built up over several years.
→ United Kingdom: Treat the provider as execution support for a material-controls environment
UK readers, especially across larger estates, campuses, or public and charity environments, should prioritize provider consistency, strong exception management, and reporting that is ready for board-level review. The 2024 UK Corporate Governance Code has been applied since 1 January 2025, with Provision 29 applicable from 1 January 2026, so evidence around material controls and unresolved exceptions matters more than generic service promises.
Useful UK angle: A multi-campus estate that needs site-wise outputs and unresolved-exception visibility before year-end control review.
→ South Africa: Require report-heavy deliverables from day one
South African public-entity and municipal procurement material is unusually concrete about what the provider should produce: asset-status reports with location and condition, support for aligning the register to the trial balance, audit-query support, PFMA/GRAP alignment, and, in some cases, office-wise location reports plus damaged/missing schedules. That makes South Africa the clearest market for a deliverables-led outsourcing article.
Useful South Africa angle: A municipality or public entity that needs office-wise location reports, missing-asset schedules, and GRAP-ready reconciliation support.
Key takeaways
- Outsource when the asset base is too distributed, the deadline is too tight, the register is too weak, or the organization needs specialist field capacity and stronger evidence quality.
- Do not outsource simply because the process feels messy. If policy, ownership, or approval logic is missing, a vendor alone will not fix governance.
- The right provider should deliver more than a count sheet: scope control, discrepancy logs, action tracking, ERP/CMMS-ready data, and audit-ready documentation.
- Full-service, hybrid, and recurring models each fit different environments.
- Most importantly, outsourcing execution does not outsource management accountability for controls, approvals, and book treatment.
Conclusion
Fixed asset verification services are most valuable when they remove execution bottlenecks without weakening governance. The right provider should bring cleanup discipline, field capacity, controlled evidence capture, useful reports, and system-ready data handoff. At the same time, management should still own the policy, approvals, and final record treatment.
This is where the distinction between service delivery and software capability becomes important. Some providers focus on end-to-end execution, including fieldwork, documentation, and data handover, while others emphasize platforms for discrepancy tracking, reconciliation, and ongoing asset management. Buyers should first determine the operating model that fits their requirements, whether project-based verification, continuous tracking, or a combination, before selecting a provider or tool.
FAQs
Q1: Is tagging always part of the service?
Ans: No. Some engagements are verify-only, while others combine tagging, verification, reconciliation, and register creation. Wishtree and AssetCues both show that tagging is a common—but not universal—service component.
Q2: Should the provider update the fixed asset register directly?
Ans Usually, the safer model is for the provider to prepare structured updates and recommendations while finance or controllership approves the final book treatment and posts the changes. Management accountability does not disappear because a vendor is involved.
Q3: Can outsourced teams work with internal teams?
Ans Yes. Hybrid models are common and often effective because internal teams know the site, and the provider brings structure, tools, QA, and surge capacity. AssetCues and its older company-selection article both describe hybrid or modular delivery options.
Q4: How should pricing be evaluated?
Ans Look beyond the unit rate. Cheap pricing often excludes cleanup, rechecks, blocked-access handling, or system-ready handoff. Compare what is truly included, how rework is billed, and what acceptance criteria define project completion.








![Fixed_Asset_Verification_A_Complete_Guide_to_Physical Asset Audits[1] Fixed_Asset_Verification_A_Complete_Guide_to_Physical-Asset-Audits](https://d1pj1zqgt7za9d.cloudfront.net/wp-content/uploads/2025/07/15124835/Fixed_Asset_Verification_A_Complete_Guide_to_Physical-Asset-Audits1.jpg)

