Introduction
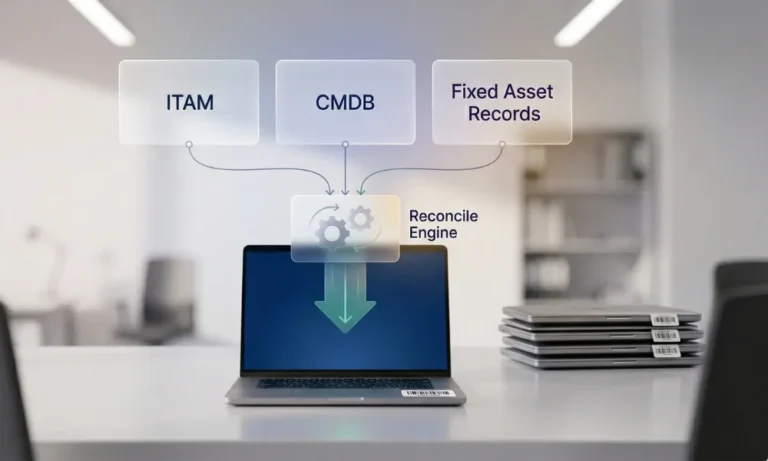
Struggling to explain why IT says a laptop is active, the CMDB shows its CI as retired, and finance is still depreciating it? This guide shows IT asset verification and how to reconcile ITAM, CMDB, procurement, endpoint, HR, and fixed asset records without turning every mismatch into an audit fire drill.
IT asset verification is the process of confirming that physical IT assets—such as laptops, servers, network gear, and shared devices—exist, are correctly assigned, and are accurately reflected across key systems. Understanding what fixed asset verification means and how the end-to-end verification cycle works provides the context for why this matters specifically in IT environments. ServiceNow defines IT asset management as the lifecycle process of tracking, deploying, maintaining, and retiring IT assets while integrating financial, inventory, and contractual data. Its CMDB, by contrast, is a repository focused on configuration items and their relationships.
In this guide, you’ll learn:
- What IT asset verification means in practice, and how it connects physical devices with ITAM, CMDB, and financial records to maintain a consistent, audit-ready view.
- Why IT asset verification is more complex than standard fixed asset verification, especially due to device movement, user assignments, lifecycle changes, and remote work environments.
- Which systems need to align—and whether they should match exactly—along with how field mapping helps reconcile differences without forcing uniform data.
- What common reconciliation mismatches look like in IT environments, and how clear ownership and rules help resolve issues like status gaps, missing assets, and lifecycle inconsistencies.
What is IT asset verification?
IT asset verification is the process of confirming that physical IT assets exist, can be uniquely identified, are assigned to the right user or location, and are represented correctly in the digital systems that govern them. For this topic, the relevant systems are not just the ITAM platform. They usually include the CMDB, procurement/receiving data, endpoint-management or discovery data, HR joiner-mover-leaver records, and the fixed asset register or ERP sub-ledger. ServiceNow’s ITAM definition explicitly includes financial, inventory, and contractual data, while its CMDB definition emphasizes relationships across the IT environment. That is exactly why reconciliation matters.
Why is IT asset verification harder than generic fixed asset verification?
IT asset verification is harder because IT assets are unusually mobile, user-linked, and lifecycle-heavy. Laptops move between users, loaners replace broken devices, docking stations get separated from base devices, servers are de-racked, network gear changes service owners, and remote or hybrid work weakens simple site-based controls. Your own live IT inventory and ITAM lifecycle pages already point to the same challenges: fragmented processes, inventory drift, remote and hybrid work, lifecycle workflows, and the need to align asset data with a CMDB and wider ITIL practices.
That is also why a fixed asset mindset alone is not enough. A finance-led register cares about cost, capitalization, depreciation, and disposal. A CMDB cares about CIs, dependencies, and operational relationships. An ITAM tool cares about inventory, deployment, warranty, lifecycle, and optimization. Each is valid. The problem starts when teams expect them to behave like the same database. ServiceNow’s own asset/CI guidance says assets focus on the financial aspects of ownership, while CIs in the CMDB track operational items and their states.
Which systems need to agree?
The table below is the core system-of-record map this spoke should own. It translates the distinctions already described in ServiceNow’s ITAM/CMDB documentation, Atlassian’s CMDB-vs-ITAM guidance, Microsoft Intune’s device-inventory capabilities, and your live AssetCues pages into one practical reconciliation model.
System |
What it should answer |
Typical golden-key fields |
Common blind spot |
|---|---|---|---|
| Procurement/receiving | Was this item ordered, received, and approved? | PO, invoice, receipt, vendor, order line, serial if captured | The device arrives, but never becomes a governed asset record |
| ITAM / hardware asset system | What physical IT asset do we own or control, who uses it, and what lifecycle state is it in? | Asset tag, serial, model, custodian, location, warranty, lifecycle status | Strong on inventory, weaker on service relationships |
| CMDB | Which configuration item supports which service, and how do dependencies relate? | CI ID, hostname, service owner, install status, hardware status, relationships | Strong on service context, not a finance ledger |
| Endpoint/discovery / MDM tool | Was the device seen, enrolled, or reporting recently? | Device ID, serial, hostname, last seen, hardware properties | Live telemetry is not the same as physical custody evidence |
| HR / joiner-mover-leaver source | Which user or department should currently hold responsibility? | Employee ID, department, location, manager, employment status | Often disconnected from the actual handover event |
| Fixed asset register / ERP | Should this item be capitalized, depreciated, transferred, impaired, or disposed? | Fixed asset ID, capitalization date, cost, NBV, cost center, disposal status | Strong on accounting truth, weaker on operational detail |
Should ITAM, CMDB, and fixed asset records ever match exactly?
No. They should align where control depends on shared truth, but they should not match on every field. Atlassian makes this distinction clearly: ITAM is about inventory and lifecycle, while CMDB is about configuration items and relationships. It also notes that not everything in ITAM belongs in the CMDB. ServiceNow makes the same point from a different angle: assets focus on financial aspects, while CIs track operational states and availability. The same logic extends to finance. Not every ITAM asset belongs in the fixed asset register, because some items are expensed, pooled, low-value, or operationally useful but not capitalized.
A good rule is simple: Shared control fields should reconcile; purpose-specific fields may differ by design.
Set of assets rules by asset type
Set Of Assets |
ITAM |
CMDB |
Fixed asset record |
Why |
|---|---|---|---|---|
| Capitalized laptops, servers, and network gear | Usually yes | Often yes | Yes | These assets have both operational and financial relevance |
| Shared monitors, headsets, and low-value accessories | Usually yes | Often no | Depends on capitalization policy | Operationally visible, not always financially capitalized |
| Loaners and repair-stock devices | Yes | Sometimes | Sometimes | High custody value, variable finance treatment |
| SaaS licenses and subscriptions | Often yes in SAM/ITAM | Sometimes, as a service/application context | Usually no as PPE | Not physical fixed assets |
| Virtual machines, apps, cloud services | Sometimes | Often yes | No as PPE | Operational CIs, not physical fixed assets |
| Expensed peripherals | Yes if tracked | Usually no | No | Useful for security and custody, not fixed-asset accounting |
Original contribution: The field-mapping model
The most useful thing this page can add is not another generic definition. It is a practical answer to the question, “Which fields must match, which should map, and which can differ?” ServiceNow’s asset/CI documentation already shows that synchronization is not always one-to-one; it explicitly says asset states and CI statuses map to their “most logical counterpart” rather than matching perfectly, and it highlights synchronized fields such as asset tag, assigned to, location, model, and warranty expiration. That principle is exactly what finance-side reconciliation needs to.
Data field |
Should match exactly? |
Can you map logically? |
Can it differ by design? |
Primary owner |
|---|---|---|---|---|
| Serial number | Yes, where captured | — | Only if the asset was repaired/reboarded under controlled history | ITAM / receiving |
| Asset tag | Yes, across physical record, ITAM, and verification output | — | May be absent in CMDB or MDM | ITAM / asset team |
| Model/manufacturer | Preferably | Yes | CMDB may normalize names differently | ITAM / CMDB |
| Assigned user/custodian | Preferably for user-assigned devices | Yes | CMDB may store the service owner or support group instead | ITAM / HR |
| Location | At the agreed hierarchy level | Yes | Finance may store cost center/site, while IT stores room/rack | IT + finance |
| Lifecycle status | — | Yes, via translation table | Status labels differ across tools | ITAM / CMDB / finance |
| Purchase date/vendor / PO | Preferably | Yes | CMDB may not need it | Procurement/finance |
| Capitalization flag / fixed asset ID | — | Limited | Yes, only finance should decide capitalization truth | Finance |
| Depreciation / NBV / disposal accounting | No need for outside finance | — | Yes | Finance |
| Service relationship/dependency | No need outside CMDB | — | Yes | CMDB / IT operations |
| Last seen / device compliance telemetry | No need for outside endpoint tools | — | Yes | Endpoint/security team |
Force exact matching only where the same physical device is being described; use mapping tables where the systems use different status vocabularies; and allow purpose-specific fields to stay purpose-specific.
How do we track IT assets for audits when systems disagree?
Use a controlled six-step reconciliation process that works for both ITAM and finance teams, rather than focusing on just one perspective. A typical workflow includes importing the working asset population, assigning verification tasks, capturing evidence, routing discrepancies for review, and syncing approved outcomes back into core systems, ensuring consistency between field activity and financial records

-
Define the in-scope IT population
Start by deciding which IT assets should reconcile all the way to finance. That usually includes capitalized laptops, desktops, servers, network hardware, major printers, specialized endpoints, and certain OT/industrial devices. It usually excludes many low-value peripherals, consumables, and non-PPE software items unless your internal policy says otherwise.
-
Establish the golden keys
Choose the fields that uniquely identify the device across systems. In most environments, those are:
-
- Serial number.
- Asset tag.
- Fixed asset ID for capitalized items.
- Hostname or CI ID where relevant.
- PO / receipt reference when cleanup is needed.
-
Freeze the working extracts
Take one controlled extract from each source:
-
- ITAM.
- CMDB.
- Endpoint/MDM or discovery.
- Procurement/receiving.
- HR or user-assignment source.
- Fixed asset register / ERP.
Do not let every team reconcile against a different export.
-
Verify by asset class
Not all IT assets need the same evidence.
Asset class |
Minimum verification proof |
What else to reconcile |
|---|---|---|
| User-assigned laptops/desktops | Serial or asset-tag match + current user/department confirmation | ITAM user, HR status, finance status, location |
| Data-center hardware | Serial + room/rack/U-position + service owner | CMDB CI, hostname, support group, finance asset ID |
| Shared devices/loaners | Serial or tag + pool location + current holder if checked out | checkout log, last return, replacement history |
| Network gear | Serial + room/rack/site + support owner | CMDB relationship, service impact, and finance record |
| Low-risk peripherals | Sample-based or room/pool control | policy threshold, expensed vs capitalized treatment |
-
Classify discrepancies fast
Use controlled categories, not free-text notes:
-
- Matched.
- Wrong user or custodian.
- Wrong location.
- Active in IT, absent in finance.
- Capitalized in finance, not deployed in IT.
- Retired in IT, open in finance.
- CI exists, but there is no valid asset link.
- Loaner/repair/swap history gap.
- Peripheral or expensed item outside the finance scope.
-
Sync only approved outcomes
Once owners approve the result, update the right systems in the right order. AssetCues’ software positioning is useful here because it emphasizes discrepancy resolution and sync back into ERP or CMDB, while ServiceNow’s asset/CI docs make clear that mapped records can synchronize state and field changes between assets and CIs.
How do you verify remote or hybrid-user devices?
Remote-device verification needs a blended control model. Microsoft Intune can collect hardware properties from managed Windows devices, which is useful for confirming that a device is enrolled, active, and technically present in the management estate. However, that data is still device telemetry, not a physical sighting or custody confirmation. Therefore, for higher-risk or higher-value remote devices, teams usually need a mix of endpoint status, user confirmation, shipment or return proof, and targeted physical spot checks. That second point is an operational inference from the limits of device-inventory data, not a Microsoft policy statement.
A practical remote-device control stack
Control |
What it proves |
Limitation |
|---|---|---|
| MDM / endpoint last seen | The device is enrolled and has been recently active | Does not prove physical condition or exact possession |
| User acknowledgment | The assigned employee confirms custody | Can be inaccurate without periodic checks |
| Shipment/return record | Device moved to or from a person/site | Does not prove the present condition today |
| Photo or video confirmation | Stronger proof for selected cases | Higher-friction control |
| Spot physical audit on return/office visit | Strongest direct confirmation | Not continuous |
What reconciliation rules resolve the most common mismatches?
This is where most IT-verification pages stay too vague. The table below is the operational rulebook this spoke should own.
Mismatch |
What it usually means |
Primary owner |
Required action |
|---|---|---|---|
| ITAM shows “in use,” and FAR has no asset | Missed capitalization, local buy, or delayed posting | Finance + procurement + ITAM | Validate threshold, ownership, and posting |
| FAR shows asset active, ITAM says “in stock” or “never deployed.” | Delayed deployment or stale finance record | Finance + ITAM | Confirm the put-to-use date and status |
| ITAM shows retired, FAR still depreciating | Disposal workflow gap | Finance + ITAM | Complete disposal, write-off, or transfer approval |
| CMDB CI exists, no linked ITAM asset | Discovery or service modeling without lifecycle ownership | CMDB owner + ITAM | Decide whether the CI needs an asset link |
| ITAM asset exists, but the CMDB CI is missing | The device is financially or operationally tracked but not service-modeled | ITAM + service owner | Create CI only if it supports a service/dependency use case |
| Assigned user changed in one system only | Joiner-mover-leaver handover failure | HR + ITAM + manager | Update user, department, and custody evidence |
| Loaner or swap replaced the serial; the old device is still active elsewhere | Swap history is not controlled | IT support + ITAM + finance | Close old record, open new linked history |
| Peripheral tracked in ITAM but absent from finance | Valid difference under capitalization policy | ITAM + finance policy owner | Mark as non-capitalized and stop treating it as a finance exception |
ServiceNow’s asset/CI sync rules are helpful here because they show that state translation is inherently mapped rather than literal. That is a strong reminder to build a status-translation table instead of expecting raw labels from ITAM, CMDB, and finance to line up automatically.
Who should own joins, moves, repairs, swaps, and disposals?
Ownership should be shared, but accountability should be explicit. Your cluster blueprint for this topic already points toward a cross-functional RACI, and that is exactly the right direction: IT owns much of the operational truth, finance owns capitalization and reporting truth, procurement shapes inbound record quality, and HR affects user-assignment quality. Meanwhile, management still owns the broader control environment under the US, India, and UK governance frameworks discussed below.
Joiner-mover-leaver and lifecycle control matrix
Event |
IT / ITAM action |
CMDB action |
Finance action |
Evidence to retain |
|---|---|---|---|---|
| New purchase received | Tag, record serial, classify asset | Create CI if service-relevant | Capitalize if the threshold and policy apply | PO, receipt, tag, serial |
| Device issued to employee | Assign user, location, status | Update owner/support context if relevant | Update the cost center if the policy requires | user acknowledgment |
| Employee transfer/move | Change user/department/site | Update CI owner/service context if needed | Update location or cost center if financially relevant | manager approval |
| Repair/swap | Preserve serial history and replacement record | Update CI state / related CI if replaced | Keep the finance record aligned with the actual capitalized unit | repair/swap log |
| Loaner issued | Move to a temporary holder/loaner state | Usually no permanent CI change unless modeled | Usually, no financial change | sign-out/return log |
| Retirement/disposal | Mark retired, collect wipe/return proof | Retire or dispose of CI | Process disposal/write-off / NBV treatment | disposal approval + certificate |
| Employee exit | Recover or confirm the disposition of assigned hardware | Update CI ownership/status | Flag unresolved items before final settlement if policy requires | exit checklist |
Country-specific control notes

→ USA: Treat IT asset reconciliation as control evidence, not just inventory hygiene
US issuers and control-focused private organizations should focus beyond keeping asset lists tidy, emphasizing control integrity and audit-ready evidence. SEC rules require management’s annual internal-control report to include management responsibility, the framework used, and management’s assessment of effectiveness, with evidential matter maintained to support that assessment. That makes unresolved gaps between ITAM, CMDB, and finance more than a data-cleanup issue when high-value or portable IT assets are material.
→ India: Focus on reasonable intervals and book treatment
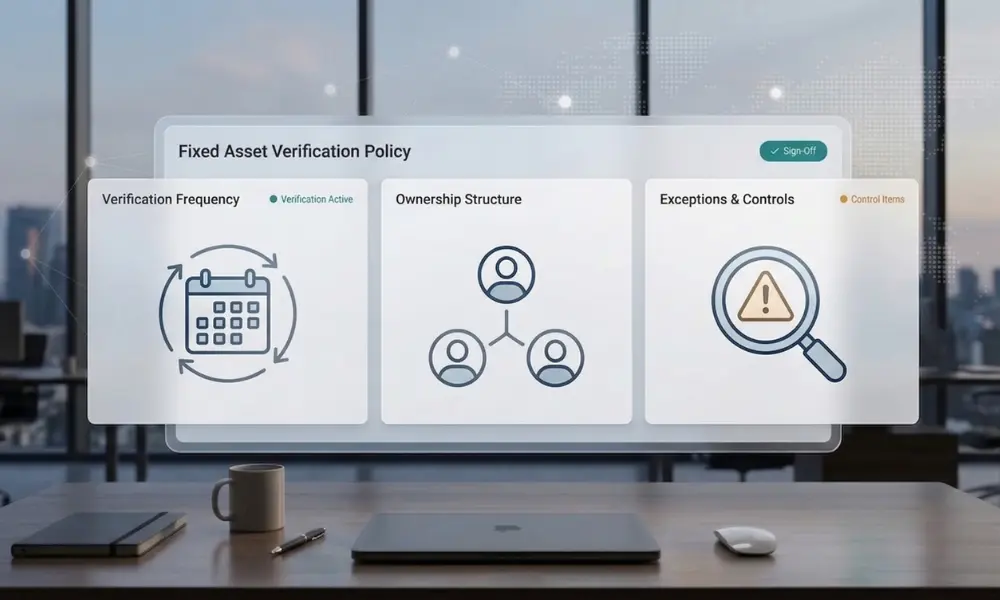
India-facing readers should treat CARO guidance as the practical anchor. It says physical verification of assets is management’s responsibility, requires adequate evidence, and explains that “reasonable intervals” depend on asset count, nature, value, verification difficulty, and geographic spread. For IT estates with branches, plants, and mobile-user populations, that makes risk-based verification and clean discrepancy treatment in the books is especially important.
→ United Kingdom: Frame this as material-controls evidence for portable and desirable IT assets
UK readers should note that the 2024 UK Corporate Governance Code has applied since 1 January 2025, with Provision 29 effective for financial years beginning on or after 1 January 2026. That makes portable and desirable IT assets especially relevant where fixed-asset and operational controls may be material. A reconciliation page that shows unresolved status gaps, remote-user exceptions, and disposal backlogs can therefore support the wider control-review conversation.
→ South Africa: design for report-heavy, audit-support outputs
South African public-entity requirements are often more concrete than private-sector blogs imply. Recent public documents call for verification outputs that confirm existence, location, ownership, completeness, and accuracy, plus barcode or serial number, condition, custodian, useful life remaining, and whether assets are in use, idle, damaged, or obsolete. Other RFQs also require asset-status reports, trial-balance alignment, and audit-query support. That makes structured IT-asset reconciliation especially valuable in public-entity environments.
Key Takeaways
- IT asset verification is harder than generic fixed asset verification because devices move faster, change users more often, and pass through more lifecycle events.
- ITAM, CMDB, and fixed asset records should align on identity, lifecycle state, owner/custodian, and disposition status for in-scope physical assets.
- They should not match on every field, because each system serves a different purpose.
- Remote-user and hybrid-workforce devices need more than system telemetry if you want audit-grade custody evidence.
- The cleanest design uses one reconciliation model, one state-translation table, and one approval path for disposals, swaps, repairs, and returns.
- This page focuses on cross-system alignment. It does not replace your cluster pages on field process, evidence sufficiency, policy, reporting, services, software, or technology design.
Conclusion
IT asset verification works best when teams stop asking one system to do every job. ITAM manages lifecycle and inventory truth. The CMDB manages configuration and dependency truth. Endpoint tools provide operational telemetry. Finance manages capitalization and accounting truth. The goal is not to flatten all of that into one table. The goal is to reconcile the shared control fields, govern the handoffs, and close the lifecycle gaps that create audit, security, and reporting risk.
That is also the natural commercial handoff for AssetCues. The fixed asset verification software already emphasizes register import, mobile verification, discrepancy handling, audit logs, and sync back into ERP or CMDB, while related product pages emphasize IT-finance reconciliation, HR/ITSM integrations, and employee-asset controls.
FAQs
Q1: How do you verify remote-user devices?
Ans: Use a mix of endpoint status, user confirmation, shipment or return controls, and targeted physical spot checks where risk is higher. Device-inventory tools help, but they do not fully replace physical or custody evidence.
Q2: What is the biggest reconciliation issue?
Ans: The most common issue is a status mismatch. An asset appears active in one system but retired, missing, transferred, or never capitalized in another system.
Q3: How often should laptops be verified?
Ans: That depends on policy, risk, and mobility. Portable, user-assigned assets usually need a tighter cadence or more frequent spot checks than fixed data-center equipment. Your live hardware-inventory page already recommends continuous updates, plus annual audits and quarterly spot checks.
Q4: Can MDM or endpoint-management data replace physical verification?
Ans: Not fully. Endpoint tools can confirm device properties and recent activity, which is valuable, but they do not always prove physical condition, exact custody, or whether the device is still where policy says it should be.
Q5: What should happen when an IT asset is retired?
Ans: IT, CMDB, and finance records should all be updated through a controlled workflow. That means the device status changes operationally, the CI is dispositioned where relevant, and finance processes disposal or write-off based on approved evidence.









![Fixed_Asset_Verification_A_Complete_Guide_to_Physical Asset Audits[1] Fixed_Asset_Verification_A_Complete_Guide_to_Physical-Asset-Audits](https://d1pj1zqgt7za9d.cloudfront.net/wp-content/uploads/2025/07/15124835/Fixed_Asset_Verification_A_Complete_Guide_to_Physical-Asset-Audits1.jpg)

